A new form of cyberattack has been developed which highlights the potential future ramifications of digital assaults against the biological research sector. Although this research was published over a year ago, in November 2020, it highlights the potential dangers of new ‘biohacking’ techniques.
In their research, academics from the Ben-Gurion University of the Negev described how “unwitting” biologists and scientists could become victims of cyberattacks designed to take biological warfare to another level.
Let’s not lose touch…Your Government and Big Tech are actively trying to censor the information reported by The Exposé to serve their own needs. Subscribe to our emails now to make sure you receive the latest uncensored news in your inbox…
At a time when scientists worldwide were pushing ahead with the development of potential vaccines to combat the “Covid pandemic,” Ben-Gurion’s team said that it is no longer the case that a threat actor needs physical access to a “dangerous” substance to produce or deliver it — instead, scientists could be tricked into producing toxins or synthetic viruses on their behalf through targeted cyberattacks.
Related: Human biohacking: an exciting prospect, but only for the rich?
The research, ‘Increased cyberbiosecurity for DNA synthesis’, was published online at the end of November 2020 and published in the December issue of the academic journal Nature Biotechnology under the title ‘Cyberbiosecurity: Remote DNA Injection Threat in Synthetic Biology’.
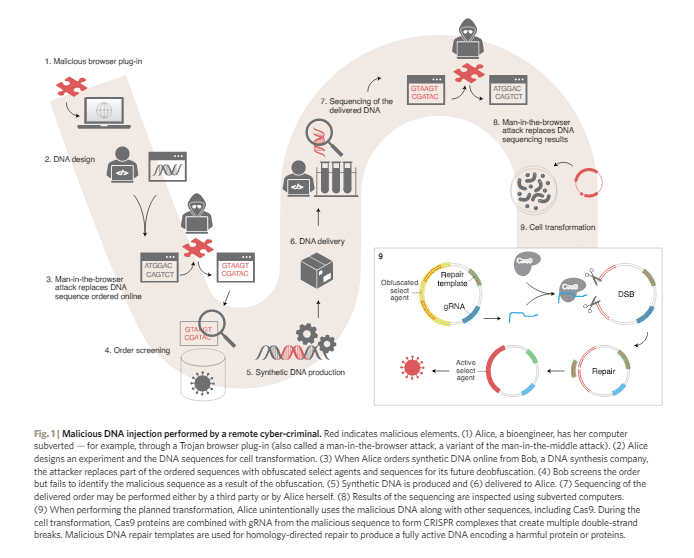
The attack documents how malware, used to infiltrate a biologist’s computer, could replace sub-strings in DNA sequencing. Specifically, weaknesses in the Screening Framework Guidance for Providers of Synthetic Double-Stranded DNA and Harmonised Screening Protocol v2.0 systems “enable protocols to be circumvented using a generic obfuscation procedure.”
When DNA orders are made to synthetic gene providers, US Department of Health and Human Services (“HHS”) guidance requires screening protocols to be in place to scan for potentially harmful DNA.
However, it was possible for the team to circumvent these protocols through obfuscation, in which 16 out of 50 obfuscated DNA samples were not detected against ‘best match’ DNA screening.
Software used to design and manage synthetic DNA projects may also be susceptible to man-in-the-browser attacks that can be used to inject arbitrary DNA strings into genetic orders, facilitating what the team calls an “end-to-end cyber biological attack.”
The synthetic gene engineering pipeline offered by these systems can be tampered with in browser-based attacks. Remote hackers could use malicious browser plug-ins, for example, to “inject obfuscated pathogenic DNA into an online order of synthetic genes.”
In a case demonstrating the possibilities of this attack, the team cited residue Cas9 protein, using malware to transform this sequence into active pathogens. Cas9 protein, when using CRISPR protocols, can be exploited to “deobfuscate malicious DNA within the host cells,” according to the team.
For an unwitting scientist processing the sequence, this could mean the accidental creation of dangerous substances, including synthetic viruses or toxic material.
“To regulate both intentional and unintentional generation of dangerous substances, most synthetic gene providers screen DNA orders which is currently the most effective line of defence against such attacks,” commented Rami Puzis, head of the BGU Complex Networks Analysis Lab. “Unfortunately, the screening guidelines have not been adapted to reflect recent developments in synthetic biology and cyberwarfare.”
A potential attack chain is outlined below:
“This attack scenario underscores the need to harden the synthetic DNA supply chain with protections against cyber biological threats,” Puzis added. “To address these threats, we propose an improved screening algorithm that takes into account in vivo gene editing.”
Republished from ZD Net, 30 November 2020
Further resources
Below is a link to a compiled list of summaries and resources which includes 81 sources together representing the knowledge base on cyberbiosecurity, as of 6 October 2020, resulting from the workshop, ‘Securing Agriculture, Food, and its Economy (SAFE) with Cyberbiosecurity’ hosted by Virginia Tech, continuing and professional education.
The Expose Urgently Needs Your Help…
Can you please help to keep the lights on with The Expose’s honest, reliable, powerful and truthful journalism?
Your Government & Big Tech organisations
try to silence & shut down The Expose.
So we need your help to ensure
we can continue to bring you the
facts the mainstream refuses to.
The government does not fund us
to publish lies and propaganda on their
behalf like the Mainstream Media.
Instead, we rely solely on your support. So
please support us in our efforts to bring
you honest, reliable, investigative journalism
today. It’s secure, quick and easy.
Please choose your preferred method below to show your support.
Categories: Breaking News, World News

Dr. Robert Malone on posted irrefutable proof of the Ivermectin success story in India. Ivermectin needs to be allowed for medical use and for doctors to prescribe it immediately in United States. It is an act of criminal malfeasance to keep up the sham in the face of overwhelming proof and overwhelming harm to the people of this nation. If you want you can get it from https://www.ivmcures.com
DEFUND THE EXPOSE!!!
.
.
DEFUND THE EXPOSE AND GET THE CHAMPAGNE OPPOSITION OUT OF HERE!!!!!!
Do you an follow BBC or CNN much?